Your Car’s Secret Backdoor: A Modern Guide to Vehicle Theft

In this highly digitalized age, the largest danger to your car might not be broken windows or forced doors. Rather, contemporary thieves use sophisticated technology to steal cars without making noise and in a very short time, usually less than two minutes. They use these concealed vulnerabilities to change conveniences into a liability and pose a risk that most drivers will never in their lifetime think of as a problem.
Knowing the New Threat Landscape
- Emergence of technological-based vehicle theft
- More dependence on car systems that are digital
- Specialised hacking tools used by criminals
- Quick thefts that cause less physical damage
- Increasing world-wide security concerns about cars
This is not about instilling fear but rather the creation of awareness and confidence. Knowing these modern theft methods will enable you to take sensible measures to secure your car. Since the days of hidden diagnostic ports to wireless key signals, the contemporary dangers demand more intelligent solutions. Having the correct knowledge and equipment, it is much easier and efficient to protect your car.

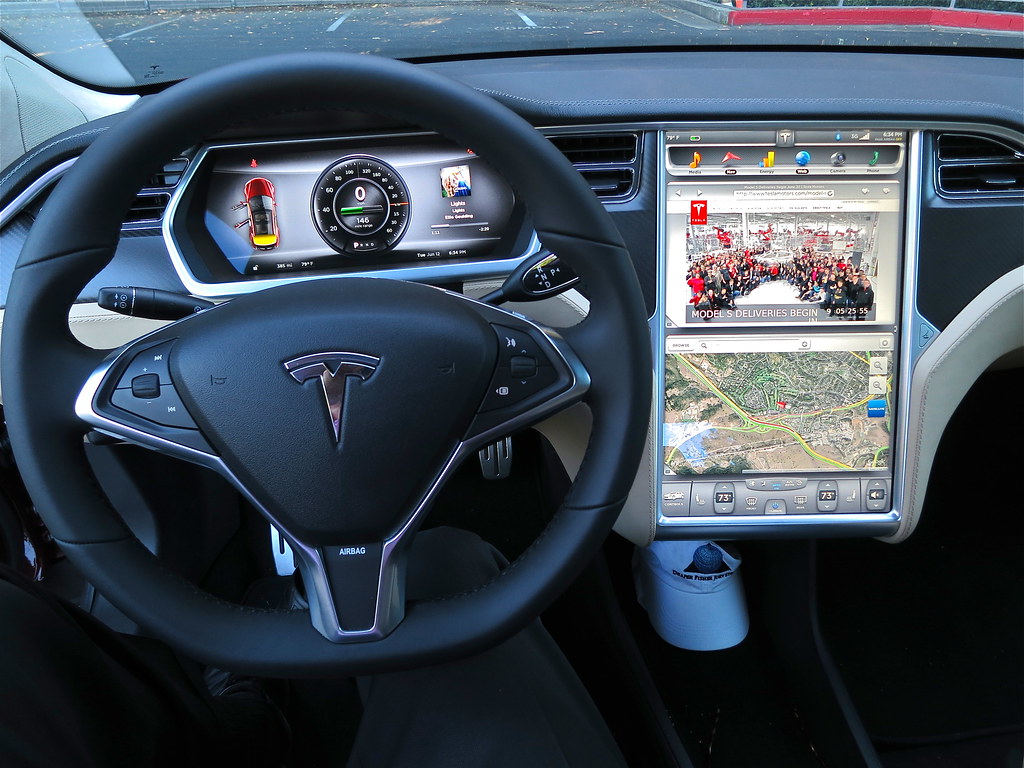
1. The Unknown Menace: OBD-II Port Exploitation
There is a little yet mighty connection point in the middle of your dashboard, which is referred to as the On-Board Diagnostics II (OBD-II) port. Initially created to assist mechanics in troubleshooting and revising software, it is an important part of contemporary car maintenance. Regrettably, this very port has turned out to be a great weak point which can be easily exploited by deft robbers with frightening ease.
Using the OBD Port by Thieves
- Break into the car
- Attach hacking devices or key programmers
- Crack the security system of the vehicle
- Re-program a new key fob in minutes
- Take off leaving no trace of theft
After gaining access to the car, criminals can quickly plug in a device to the OBD-II port and modify the electronic system of the car. Within a very short period of time, they are able to generate a new key or turn off the security features. This approach entails minimal traces thus leaving the owners guessing how the theft might have taken place until it is too late.

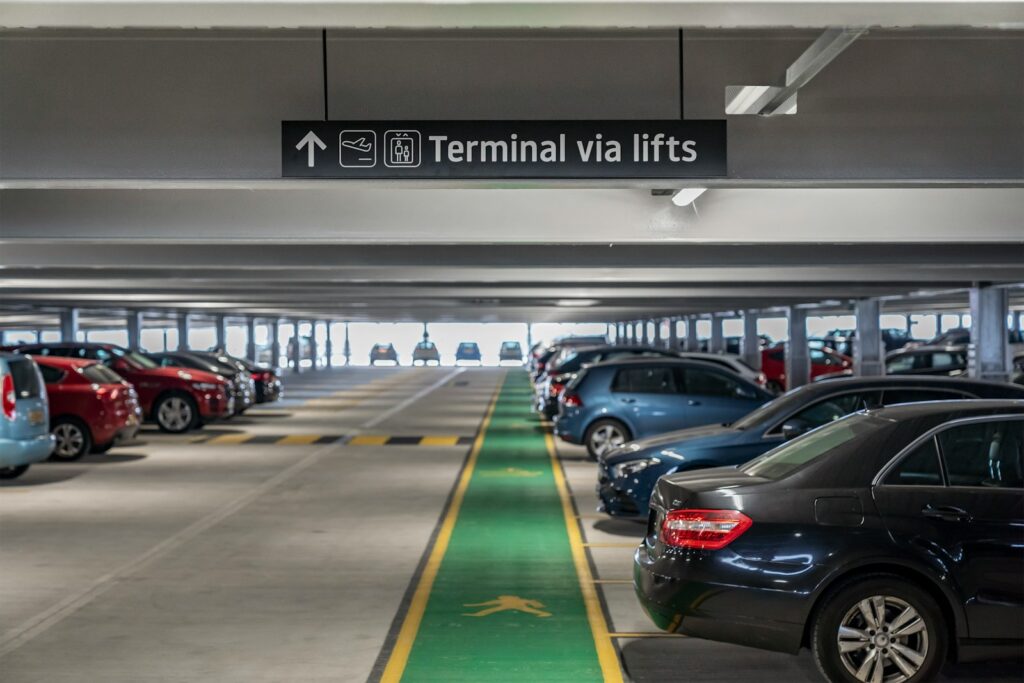
2. Theft based on OBD in the real world
This form of theft is not only hypothetical- it is occurring in large cities and is impacting thousands of drivers. Crooks attack cars in the driveway, garage and even in secure areas and seize the moment. Whole bands even work in conjunction, employing coordinated techniques to rob several vehicles within a single night in astounding ways.
Where These Thefts Are coming
- Residential driveways in urban areas
- Apartment parking garages
- Lowly monitored parking lots
- High-value vehicle neighbourhoods
- Business parking areas overnight
Such cases demonstrate the extent to which the automobile theft nowadays is organised and efficient. In most instances, cars are stolen without any form of obvious damage, which makes the owners perplexed and angry. The rate and accuracy of such operations illustrate the fact that the conventional security procedures are not sufficient to discourage the efforts of hardcore criminals.

3. Relay Attacks: Stealing by touching nothing
Although the OBD-II port is a physical vulnerability, wireless technology poses a completely new digital hazard. Relay attacks use the signal that your key fob sends at all times, and enable the burglars to unlock your car and start it, without ever needing to touch your keys again. This technique is non-verbal, quick and extremely hard to trace in real time.
Relay Attack Principles
- One of the thieves steals the signal-post on the verge of your house
- Another is close to the car and carries a relay
- amplification of signal and transmission happens immediately
- Vehicle unlocks, thinking that key is in the car
- Engine starts without alarming
It can be done in less than a minute, and it is one of the most successful methods that are applied nowadays. It takes most drivers hours before they realise that their car is missing. Since there is no physical damage, it may sometimes seem like the car has just disappeared, further contributing to the feeling of helplessness and disorientation.

4. Signal Jamming and Daily risks
Signal jamming is another popular trick with thieves intercepting the locking signal of your key fob. When the lock button is pressed and one walks away believing that his or her vehicle is locked, in the real sense it is not locked. This method works especially well in a high traffic or noisy setting where it is very easy to miss confirmation signals.
General scenarios of Signal jamming
- Parking lots of shopping centres are congested
- Distracting busy streets
- Parking during the night with low visibility
- Large events with high pedestrian traffic
- Areas where there is high vehicle turnover
Such simple circumstances enable thieves to work without detection. Habit is something that drivers tend to trust over verification, and this is an opportunity to criminals. Even a mere lapse of concentration leaves your car at full exposure showing that little negligence can have big implications.
5. Majority of the Targeted Vehicles and Technologies
Although virtually any car that is manufactured nowadays is susceptible, thieves tend to target popular or expensive models. CARS with highly developed keyless access are especially appealing targets since it means they use wireless communication. New technology in the automotive industry can pose new risks at times as they are introduced without the appropriate securing measures.
Frequently Targeted Vehicles
- Ford Fiesta and Ford Focus models
- Volkswagen Golf series
- Land Rover SUVs
- BMW and Audi cars
- Models include Toyota and Kia
Moreover, newer technologies, including integration of smartphones and the use of digital keys, are increasing the attack surface. Although these features are convenient, they demand increased security. With innovation taking place, it is important to be informed of the new threats in order to keep your vehicle safe.
6. First Line of Defense: Intelligent Habits
Simple daily habits can help you to reduce your risk greatly before you invest in the sophisticated tools. Familiarity and regularity are important in deterring theft. Simple safety measures can help you eradicate lots of easy targets criminals use when attacking vehicles.
Essential Safety Practices
- Never leave doors and windows open
- Park in safe and well-lit places
- Do not leave valuables in view
- Check and recheck locks and leave
- Do not leave keys near doors and windows
These habits might be easy to follow but they are the basis of proper vehicle security. Numerous thefts take place because of minor omissions that can be easily prevented. You can add an extra level of security by remaining vigilant and forming habitual routines that would render your car less attractive to potential thieves.

7. Signal blocking: Faraday Protection
Signal-blocking solutions provide an effective and cost-effective solution to the problem of relay attacks. Faraday pouches are specially made to shield off wireless signals, and therefore thieves will not be able to get hold of the transmission of your key fob. Such minor accessories can have great impact on securing your vehicle against digital theft techniques.
Advantages of Faraday Pouches
- Rejects all wireless key signals
- Deters health care attacks made on the relay
- Portable and convenient to use
- Low cost and readily accessible
- No technical set up is required
Faraday pouch is as easy to use as the key where you put your key when you are not using it. This will make sure that no signal can be intercepted or relayed. Together with other security features, it offers a good protection against one of the most prevalent types of car theft in the modern world.

8. Physical Deterrents Do Count
Although digital theft is on the increase, physical deterrents are very effective. Thieves will be deterred by visible security devices because they will take more time and effort to steal a car. The vast majority of criminals are opportunistic and can easily attack their victims, making any added barriers a significant deterrent.
Good Physical Security Means
- Steering wheel locks
- Pedal and brakes locks
- Parked cars wheel clamps
- Visible alarm systems
- Garage security barriers
These devices are used as physical means of protection as well as visual warnings. An obviously locked car is not appealing to the thieves who are on the lookout. Even less advanced devices might provide a resistance enough to push criminals to a less challenging target.

9. Obtaining the OBD-II Port
The OBD-II vulnerability needs to be addressed to provide a complete protection. There are a number of measures that can be taken to ensure that this vital element is not accessed unauthorised. You can prevent losing keys to thieves by restricting their access to the port, so they cannot reprogram the keys or modify the system on your vehicle.
How to protect the OBD Port
- Install a lock on a physical OBD port
- Have computerized lock systems
- Move the port to a concealed place
- Add immobiliser-based protection
- Limit access using authentication measures
These steps provide a much-needed level of protection against one of the most efficient theft techniques. By locking the port, you deny criminals one of the tools they use, and their control of your vehicle will be much harder.

10. Intelligent Security of the Future
The high-level security systems provide proactive security with intelligent technology. These solutions are used to track down and recover vehicles more efficiently, with the help of GPS tracking and the integration of smartphones. They will give immediate warnings and enable the owners to react fast to suspicious activity.
Modern Security Features
- GPS location and rescue devices
- Alerts and monitoring through smartphone
- Immobilisation and locking remotely
- Real-time motion detection
- Interoperability with law enforcement systems
These technologies are more advanced than conventional alarms with the provision of continuous surveillance. Not only do they prevent theft but they also raise the possibilities of retrieving a stolen vehicle. With smarter cars, security systems need to keep up with such advancements in order to be effective.